Advantages
Specifications
1.Turnstile System Video:
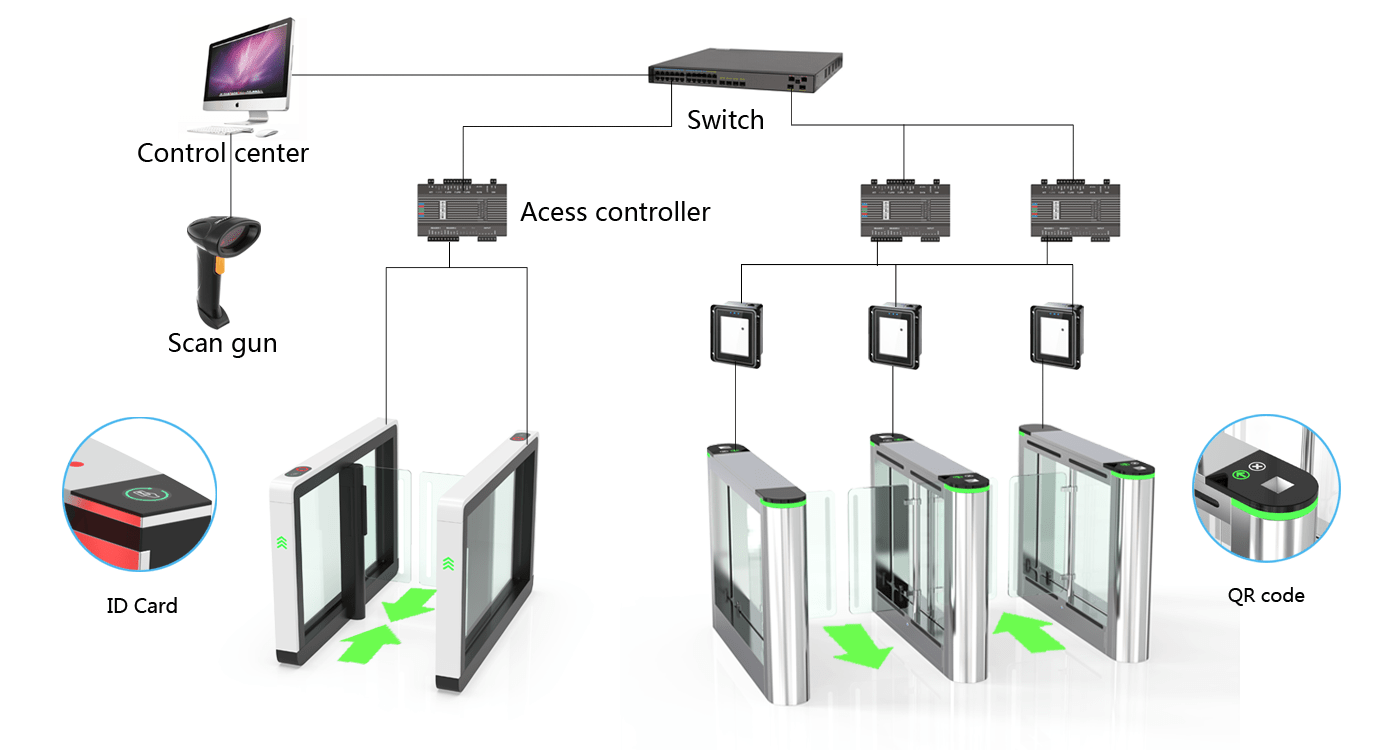
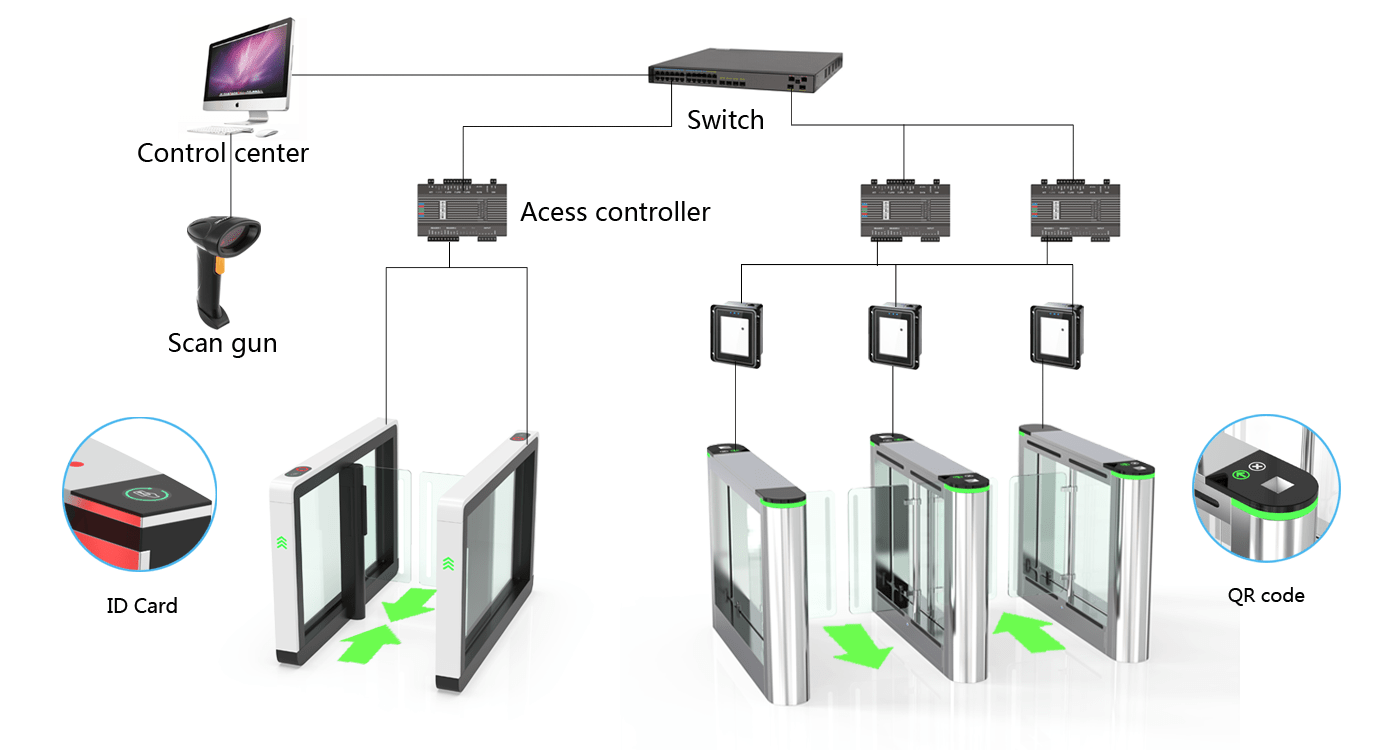
2. What is turnstile system?
The turnstile system is composed of turnstile gate and access control, usually installed at the entrance and exit of the building. When the access control installed on the turnstile gate verifies that someone's identity information (card, face or QR code) is passed, the access control will notice the turnstile gate to open through a relay signal (or 485/232 signal). When passing, the infrared installed in the turnstile gate will always be detected. When it is detected that a person has passed, the turnstile gate will be automatically closed.
3. How to design a turnstile system?
3.1System Capacity Requirements
1) Access control system capacity: The access control system has the ability to support 256 turnstile gates to facilitate the expansion of the system in the future;
2) Cardholder capacity: each turnstile gate can manage up to 40,000 cards in and out;
3) Event records: When the controller is offline from the computer, the access turnstile can save up to 40,000 latest records;
4) Capacity of workstations and operators: In order to enable the doorman, property management, control center, and related departments to monitor and manage the system in time, the system allows multiple workstations to run at the same time;
5) The system should adopt a modular design and have good scalability. The number of access guards can be expanded with the system. When the system is expanded, it only needs to access the network nearby;
6) The system controller should be a distributed database, and the relevant management and control information are stored in the memory of the relevant controller. The operation is completely independent of the influence of the communication circuit and the computer so that the system has high reliability. When it is damaged locally, it will not affect the operation of the entire system.
The turnstile system adopts network type TCP/IP networking, each turnstile gate controller has an independent network interface, which can be independently connected to the network to realize the networking function. Each controller can control the entry and exit of the 1-channel turnstile gate to open the gate by swiping the card, which can restrict the entry and exit of personnel or the entry and exit of motorcycles and bicycles to enter the designated gate only within a designated time.
In other cases, all personnel is prohibited from entering and leaving. After an alarm event occurs, the on-site alarm can be linked to the alarm or the information can be transmitted to the management center through the network. The electronic map of the management center automatically pops up on the alarm gate and informs the relevant management personnel through sound and light alarms to deal with it in time. In addition, there are the functions of anti-return, regional APB, multi-person and multi-group, and arming/disarming.
3.2 Turnstile system function
1. system authorization management can be divided into periods and levels. It can manage the time zone restrictions for personnel, each time zone can be set individually and flexibly, and each person can select multiple time zones at the same time. The system controller can manage at least 40,000 people and store at least 40,000 data records. The system has anti-submarine and anti-reverse functions; the system monitoring interface can display information such as the current entry and exit door number, the card number and name of the passer, the card reading time, and whether the passage is successful.
2. The system can store information such as system parameters and access door data, and can print through the printer;
3. Have the ability to adapt to abnormal situations. When communication with the management terminal is interrupted, the normal opening of the on-site access gate is not affected; the authorization can be canceled through the management host. Invalid and expired cards can be recycled and can be used again after reauthorization. Various event data reports can be provided, including cardholder access events, alarm events, system events, etc. The system can log the operation steps of the administrator. The event record should include the following contents: allow passage, deny passage, alarm, force open door, normally open, fault, network connection, network disconnection, and remote control. The system has a special memory protection device, and the access control code and system data will not disappear due to power failure.
3.3 Communication and lines
The management system adopts the TCP/IP protocol Ethernet LAN/WAN, and the communication with the control layer also adopts the TCP/IP protocol. The control layer and execution layer lines have fault tolerance and monitoring capabilities. When a certain point is damaged or a short circuit or open circuit occurs due to other reasons, the line fault will be reported to the center immediately, and the line will be repaired without affecting the normal operation and communication of the system.
3.4 System Security
1) All control modules of the system have a CPU, and each module can work independently when the system fails.
2) When the network cable is broken somewhere, the entire system can continue to work, and an alarm message will be issued, indicating that it should be repaired. The controller has protection function against network communication interruption, power failure, and misoperation.
3) It adopts a split structure design that fully complies with the security product specifications, that is, the card reader part and the control part are separated.
4) A watchdog circuit is added to the hardware. When the controller hardware fails and is in a crash state, the system can be automatically restarted to ensure that the entire system can work normally.
5) Equipped with a tamper-proof detection circuit, after the external iron box is illegally opened by people, it will link the on-site alarm to alarm and upload the alarm information.
6) After installing a backup battery or UPS uninterruptible power supply, it can maintain normal operation for a period of time under the condition of power failure, and will not cause danger due to the automatic opening of the power failure gate.
3.5 Software functions
1) The management software adopts the familiar window, mouse, and keyboard operation, and has detailed instructions to help and prompt the operator to operate, which is simple and convenient.
2) It has perfect database management functions and powerful retrieval functions, supports the loading of large amounts of data, and has multiple clue screening methods and clue priority screening methods.
3) The software database adopts standard SQL Server or Access database, ODBC general access interface, and provides import and export functions of Excel file format.
4) The software can classify and store system information and report content for easy search.
| Model No. |
MS11S |
| Cabinet Material |
SUS304/316 stainless steel |
| Arm Material |
SUS304/316 stainless steel |
| Unit Dimension(W*L*H) |
1400*120*980mm |
| Passing Direction |
Uni-directional/Bi-directional |
| Photoelectric Sensor |
6 Pairs |
| Passage Width |
600mm |
| Opening/Closing |
0.5 seconds |
| Flow Rate |
40-45 person/min |
| Mechanism |
Brushed/Brushless/Servo Motor
|
| Power Supply |
AC100-230V,50Hz |
| Voltage |
from the AC (100–240) V, 50/60 Hz
from a DC source 24 V |
| Application |
Indoor and outdoor(Shelter) |
| Working Temperature |
-25℃~+70℃ |
| Operation Humidity |
0 ~ 95% (No freeze) |
| MCBF |
8,000,000 cycles |
| Anti-panic mode |
Automatically open when power off |
| Communication |
Dry contact, Relay signal, RS485 |